So in this list we will be seeing the top best hacking tools for windows, Linux and/or Mac OS x users. Disclaimer: HackeRoyale is publishing this article just for educational purposes and we don’t promote malicious practices. Top Best Hacking tools for Windows, Linux & Mac: Metasploit. Metasploit is a big tool very often used for multiple. All these hacking tools 2018 provided here are effective and free of cost.We have compiled this list of top hacking tools of 2018 with their description & download links. Metasploit: Metasploit is available for all major platforms including Windows, Linux, and OS X. 13 Best Hacking Software for Windows, Linux, and Mac 1. Metasploit Best collection of exploit tools. Rather than calling Metasploit a collection of exploit tools, I’ll call it an. The software we advertise are open source. If you need to add things like Kernel Extensions, you can. Users can even ask the developers to make custom built builds of their software. OS X Hackers are is not affiliated with Apple Inc. Mac OS Ten (X), Mac, iOS, iPhone, iPad, and all other Apple product names are trademarks or registered. I believe not many of you here will even debate this, I mean even a hacker, who isn’t a.

WikiLeaks has just published a new set of classified documents linked to another CIA project, dubbed 'Imperial,' which reveals details of at least three CIA-developed hacking tools and implants designed to target computers running Apple Mac OS X and different flavours of Linux operating systems.
If you are a regular reader of THN, you must be aware that this latest revelation by the whistleblower organisation is the part of an ongoing CIA-Vault 7 leaks, marking it as the 18th batch in the series.
If you are unaware of the Vault 7 leaks, you can head on to the second of this article for having a brief look on all the leaks at once.
Achilles — Tool to Backdoor Mac OS X Disk Images
Best Hacking Tools For Macos

Dubbed Achilles, the hacking tool allows CIA operators to combine malicious Trojan applications with a legitimate Mac OS app into a disk image installer (.DMG) file.
The binding tool, the shell script is written in Bash, gives the CIA operators 'one or more desired operator specified executables' for a one-time execution.
As soon as an unsuspecting user downloads an infected disk image on his/her Apple computer, opens and installs the software, the malicious executables would also run in the background.
Afterwards, all the traces of the Achilles tool would be 'removed securely' from the downloaded application so that the file would 'exactly resemble' the original legitimate app, un-trojaned application, making it hard for the investigators and antivirus software to detect the initial infection vector.
Achilles v1.0, developed in 2011, was only tested on Mac OS X 10.6, which is Apple's Snow Leopard operating system that the company launched in 2009.

SeaPea — Stealthy Rootkit For Mac OS X Systems
The second hacking tool, called SeaPea, is a Mac OS X Rootkit that gives CIA operators stealth and tool launching capabilities by hiding important files, processes and socket connections from the users, allowing them to access Macs without victims knowledge.
Developed in 2011, the Mac OS X Rootkit works on computers running then-latest Mac OS X 10.6 (Snow Leopard) Operating System (32- or 64-bit Kernel Compatible) and Mac OS X 10.7 (Lion) Operating System.
The rootkit requires root access to be installed on a target Mac computer and cannot be removed unless the startup disk is reformatted or the infected Mac is upgraded to the next version of the operating system.

Aeris — An Automated Implant For Linux Systems
The third CIA hacking tool, dubbed Aeris, is an automated implant written in C programming language that is specifically designed to backdoor portable Linux-based Operating Systems, including Debian, CentOS, Red Hat — along with FreeBSD and Solaris.
Aeris is a builder that CIA operators can use to generate customised impacts, depending upon their covert operation.
'It supports automated file exfiltration, configurable beacon interval and jitter, stand-alone and Collide-based HTTPS LP support and SMTP protocol support — all with TLS encrypted communications with mutual authentication,'
'It's compatible with the NOD Cryptographic Specification and provides structured command and control that's similar to that used by several Windows implants.'
Previous Vault 7 CIA Leaks
Last week, WikiLeaks revealed about CIA contractor Raytheon Blackbird Technologies, which analysed in-the-wild advanced malware and hacking techniques and submitted at least five reports to the agency for help develop their own malware.
Since March, the whistle-blowing group has published 18 batches of 'Vault 7' series, which includes the latest and last week leaks, along with the following batches:
- Highrise Project — the alleged CIA project that allowed the spying agency to stealthy collect and forwarded stolen data from compromised smartphones to its server through SMS messages.
- BothanSpy and Gyrfalcon — two alleged CIA implants that allowed the spying agency to intercept and exfiltrate SSH credentials from targeted Windows and Linux operating systems using different attack vectors.
- OutlawCountry – An alleged CIA project that allowed it to hack and remotely spy on computers running the Linux operating systems.
- ELSA – the alleged CIA malware that tracks geo-location of targeted PCs and laptops running the Microsoft Windows operating system.
- Brutal Kangaroo – A tool suite for Microsoft Windows used by the agency to targets closed networks or air-gapped computers within an organization or enterprise without requiring any direct access.
- Cherry Blossom – An agency's framework, basically a remotely controllable firmware-based implant, used for monitoring the Internet activity of the targeted systems by exploiting vulnerabilities in Wi-Fi devices.
- Pandemic – A CIA's project that allowed the agency to turn Windows file servers into covert attack machines that can silently infect other computers of interest inside a targeted network.
- Athena – A CIA's spyware framework that has been designed to take full control over the infected Windows PCs remotely, and works against every version of Microsoft's Windows operating systems, from Windows XP to Windows 10.
- AfterMidnight and Assassin – Two alleged CIA malware frameworks for the Microsoft Windows platform that has been designed to monitor and report back actions on the infected remote host computer and execute malicious actions.
- Archimedes – Man-in-the-middle (MitM) attack tool allegedly created by the CIA to target computers inside a Local Area Network (LAN).
- Scribbles – A piece of software reportedly designed to embed 'web beacons' into confidential documents, allowing the agency to track insiders and whistleblowers.
- Grasshopper – Framework which allowed the spying agency to easily create custom malware for breaking into Microsoft's Windows and bypassing antivirus protection.
- Marble – Source code of a secret anti-forensic framework, basically an obfuscator or a packer used by the CIA to hide the actual source of its malware.
- Dark Matter – Hacking exploits the agency designed to target iPhones and Macs.
- Weeping Angel – Spying tool used by the agency to infiltrate smart TV's, transforming them into covert microphones.
- Year Zero – Alleged CIA hacking exploits for popular hardware and software.
When talking about different OS platforms like Windows, Linux or Mac OS X, the common term that we can get to hear is Hacking. These operating systems are easily prone to hacking and have the highest records of being hacked by professional hackers. Since it involves a great level of skill and knowledge on computer and its networks, not many of us are aware of hacking and how they actually do it. However, there exists some exciting hacking tools 2018 that are required to become a successful hacker. Here we bring you some of the best hacking tools of 2018 along with its best features. Read on the guide to make use of the information for educational purpose rather than for malicious practice. Get to know the detailed information of these best ethical hacking tools 2018 and learn how to use the hacking tools. Along with these best hacking tools for Windows, Linux and Mac OS X, also have a look at the best Android hacking apps 2018.
NetSparker
Maintaining improper security breaches means that you are keeping your business at risk in the near future. NetSparker is more than a best hacking tool as it works as a web application security tool to manage security vulnerabilities. The built-in workflow tools are designed specifically to manage the security of multiple websites. You need not buy, install any hardware or software, just launch the application from the dashboard to perform a security scan from any location. If it is unable to check any flaw, it will just warn you of something malicious activity happening. Moreover, it automatically exploits the vulnerabilities found in a safe way and even display the proof of exploitation thus warning us to use more advanced security settings.
Download NetSparker.
Nmap (Network Mapper)
The best hacking tools 2018 till date that is feature-rich and at the same offers user-friendly interface is Nmap. With its advanced tools, Nmap is sure to keep all the hackers behind. The Nmap that is called as Network Mapper is the free open source hacking tool used for network scanning and security auditing. Considering its features, the Nmap is claimed to be one of the best ethical hacking tools 2018. With thousands of admin users, Nmap has the capability to discover open ports, monitor host availability on the network and also can determine which operating system is used by the host system. This award-winning hacking tool renders its support to all major platforms like Windows, Linux and Mac OS X.
Pro Tools Mac Os
Here is how to connect remotely on Windows 10.
Download Nmap (Network Mapper).
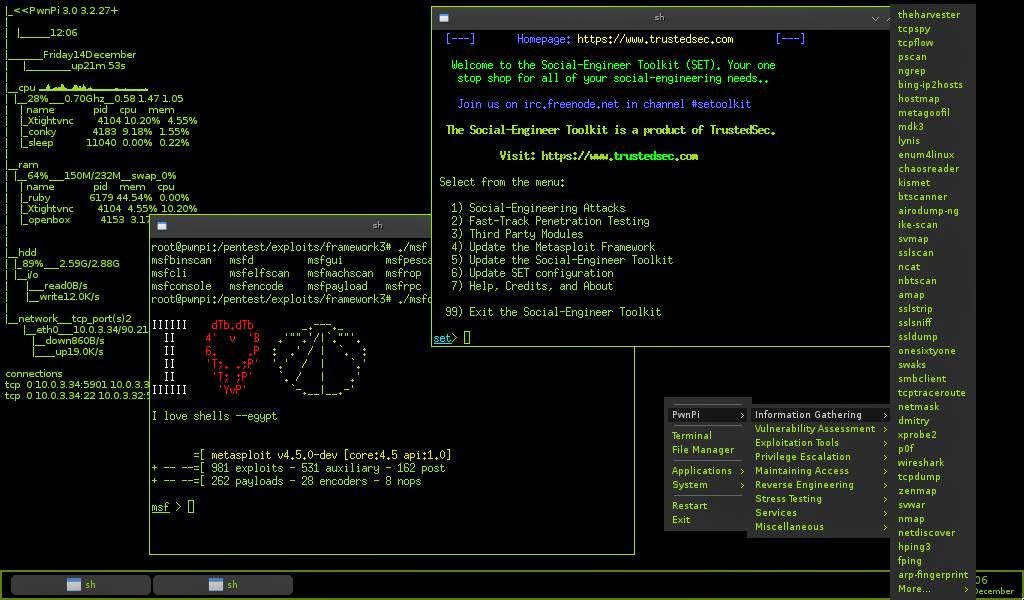
MetaSploit
The fully featured hacking tool that can hack like a pro is Metasploit. Designed for enterprise security solutions, the Metasploit can test your defence attacks on the network safely and helps to uncover all those security issues if any. Rather than calling as a Metasploit, it can be called as a collection of exploits with its own infrastructure to build its own custom tools. It is one of the popular security tools to locate vulnerabilities on Windows, Linux, Mac OS X. It can simulate the real-world attacks thus making you know about your weak points so as to fix them at priority. This tool is quite helpful for the penetration testers and for those professionals involved in IDS testing plans.
Download MetaSploit.
Wireshark
Hacking Os Download
Available for free download, the Wireshark hacking tools 2018 is a packet sniffer, packet analyzer and a password hacker. Apart from capturing and detecting network passwords, the Wireshark holds the capability to secure the network from outside intruders. Not only the offline analysis, Wireshark can also analyze data from Bluetooth, USB, Token ring, Ethernet and more. Supporting all major platforms, this is one of the best ethical hacking tools 2018 available online. It can inspect hundreds of protocols and detects best results with live capture.
Also read: How to run Windows programs without installing them.
Download Wireshark.
Maltego
Here is another best hacking tools 2018 that is available for Windows, Linux and Mac Operating system. This interactive hacking tool is used for interrogation to find the relationship between information collected from different sources. It can depict the information graphically and analyses the relationship between different entities like websites, documents, people and companies. It can enumerate network information such as DNS name, domain name, IP address, and netblocks. As for the personal information, Maltego can analyze email address, phone numbers, social groups that the person is associated with and the list of companies that the person is in connection with. It can even extract metadata from the target domain files. With the easy to use interface, you can install the Maltego setup quickly and immediately provides the graphical interface to see the relationships instantly. If your PC or laptop is running on Windows, Linux or Mac OS X then probably this is one of the best ethical hacking tools 2018 to consider.
Download Maltego.
Acunetix WVS
The automated tool that can scan web applications and resolve the exploitable vulnerabilities is Acunetix WVS. Considering the innovative features offered, this is one of the best hacking tools 2018 attracted by many hackers. Securing the web application of the company especially from the professional hackers is quite a tedious task. As the Cyber attacks are taking a rise, the need for the best ethical hacking tools 2018 has become mandatory. Here comes the need pf Acunetix WVS that is designed by keeping the threat in mind. It can scan as well as resolve any exploitable vulnerabilities. Developed by highly experienced security developers, this renders its support to all the major Operating system platforms.
Download Acunetix WVS.
Want to download the Windows latest version, then check here for Windows 10 latest version free download 2018, Lucky Patcher 7.2.9 APK Latest Version so, have a look at the best Antivirus to install for Windows 10 operating system.now it is possible to run windows programs without installing them.If ads and pop up’s are irritating you then have a look at AdBlock Vs AdBlock Plus – Which Is The Better Ad Blocker 2018.
PreviousNext




